The digital realm can be a enigmatic place. But sometimes, it can also be infested by something truly unsettling. A being, lurking in the code stream, leaving behind whispers of malfunction. It's a fear that torments many, the suspicion that they are not alone.
- Have you ever felt it? A sudden chill, a glitch in the monitor? A feeling of being followed by something unseen?
- Myths abound of this digital ghost, a phantom that harbors within the channels of information. A mysterious force, leaving behind clues of its existence.
Is it real? Or just the imaginings of a nervous mind? The mystery remains, whispering in the current of data.
Subliminal Streams: The Nuance of Concealed Broadcasting
The digital/virtual/cybernetic frontier is a vast and ever-evolving landscape, rife with opportunities for both innovation and intrigue. In this realm, where information flows like a boundless river, a new art form has emerged: silent broadcasts. These mysterious/subtle/elusive transmissions operate beneath/outside/beyond the radar of conventional detection, weaving their way into the fabric of our online/virtual/digital existence.
- Utilizing/Exploiting/Harnessing advanced encryption protocols and clever/ingenious/devious coding techniques, silent broadcasts transmit/relay/disperse messages that remain invisible/undetectable/imperceptible to the untrained eye. They are a whisper in the digital wind, a phantom signal gliding/drifting/sinking through the cacophony/noise/chatter of the internet.
- Masterminds/Hackers/Visionaries who engage in this shadowy art form employ/utilize/harness their technical prowess to create illusionary/phantom/spectral transmissions that can be accessed/decoded/perceived only by those in possession of the correct/specific/unique key.
- The implications/The potential/The consequences of silent broadcasts are vast and multifaceted, ranging/extending/spanning from mundane to profoundly impactful. They could be used for harmless/benevolent/covert purposes, such as spreading awareness/sharing information/disseminating knowledge, or they could be weaponized/manipulated/exploited for more sinister/malicious/nefarious ends.
As the digital world continues to evolve and expand, silent broadcasts will undoubtedly become an increasingly pervasive/ubiquitous/integral part of the online/virtual/cybernetic landscape. Whether they are used for good or evil remains to be seen, but one thing is certain: they represent a new frontier in the realm of information warfare, where the battle is fought not with bombs and bullets, but with code and cryptography/encryption/algorithms.
Past the Radar: Unseen and Undiscovered
In a vast sphere, countless treasures remain shrouded. These reside occurrences that veer read more away from usual awareness. They thrive independently, overlooked by the majority. These phenomena are the target of exploration for those who dare.
- Envision a world that mythology reveal themselves as reality.Where the impossible permeates truth.
- Discovering these hidden elements of existence can be an adventure filled with both difficulty and rewarding findings.
- Perhaps, there are answers to mysteries that have been untouched humanity. Perhaps , the direction to these explanations lies past the radar, waiting for the intrepid few to seek them out.
Journey to The Shadow Channel
The Secret Web, also known as the Shadow Channel, is a shadowy realm of broadcasting. Here, content flows through obscure channels, bypassing mainstream censorship. Secret communities thrive within this digital wilderness, disseminating knowledge and ideas that are often suppressed in the public world. The Shadow Channel is a double-edged sword, offering both anonymity and risk.
- Dive into the depths of this hidden network
- Unearth the truth that lie within
- Exercise caution as you navigate its dark corners
Hidden Audiences: Navigating Stealth Platforms
The digital landscape is constantly evolving, with new platforms emerging all the time. Some of these platforms operate in the shadows, attracting niche audiences who seek anonymity or restricted content. Understanding these "stealth" platforms can be a complex endeavor, requiring a different set of skills and tactics.
- First, it's essential to identify the platform's intent. What fuels its community? What type of content is shared?
- Next, explore the platform's culture. Grasp the unwritten rules that govern engagement among users.
- Finally, be conscious of your own impact. Remember that even on "stealth" platforms, there are always repercussions to your actions.
Deep Dive: The Mystery Behind Masked Streamers
The digital realm is a captivating landscape where anonymity often reigns supreme. Among the countless avatars and usernames, a particular breed of streamer has emerged – figures cloaked in absolute secrecy. These masked personalities have captivated audiences with their intriguing gameplay, leaving fans obsessed with revealing the identities hidden beneath the online facade.
Whispers spread like wildfire about these enigmatic figures, fueled by rumors and occasional glimpses of their true selves. Some believe they are ordinary people seeking anonymity, while others view them as modern-day Robin Hoods.
- Reasons behind their masked nature vary greatly.
- Perhaps they fear backlash
Whatever the motivation, these masked marvels have undeniably shaped the streaming landscape. As technology continues to evolve, so too will the landscape of hidden identities. One thing is certain: the allure of the unknown will continue to captivate audiences for years to come.
 Haley Joel Osment Then & Now!
Haley Joel Osment Then & Now! Kelly McGillis Then & Now!
Kelly McGillis Then & Now! Hailie Jade Scott Mathers Then & Now!
Hailie Jade Scott Mathers Then & Now! Nancy McKeon Then & Now!
Nancy McKeon Then & Now!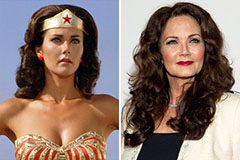 Lynda Carter Then & Now!
Lynda Carter Then & Now!